800,000 blood donors' personal data accessed illegally and possibly stolen; police investigating
Sign up now: Get ST's newsletters delivered to your inbox
A database containing the personal information of blood donors was uploaded to a server which was accessed suspiciously from several IP addresses between October 2018, and March this year.
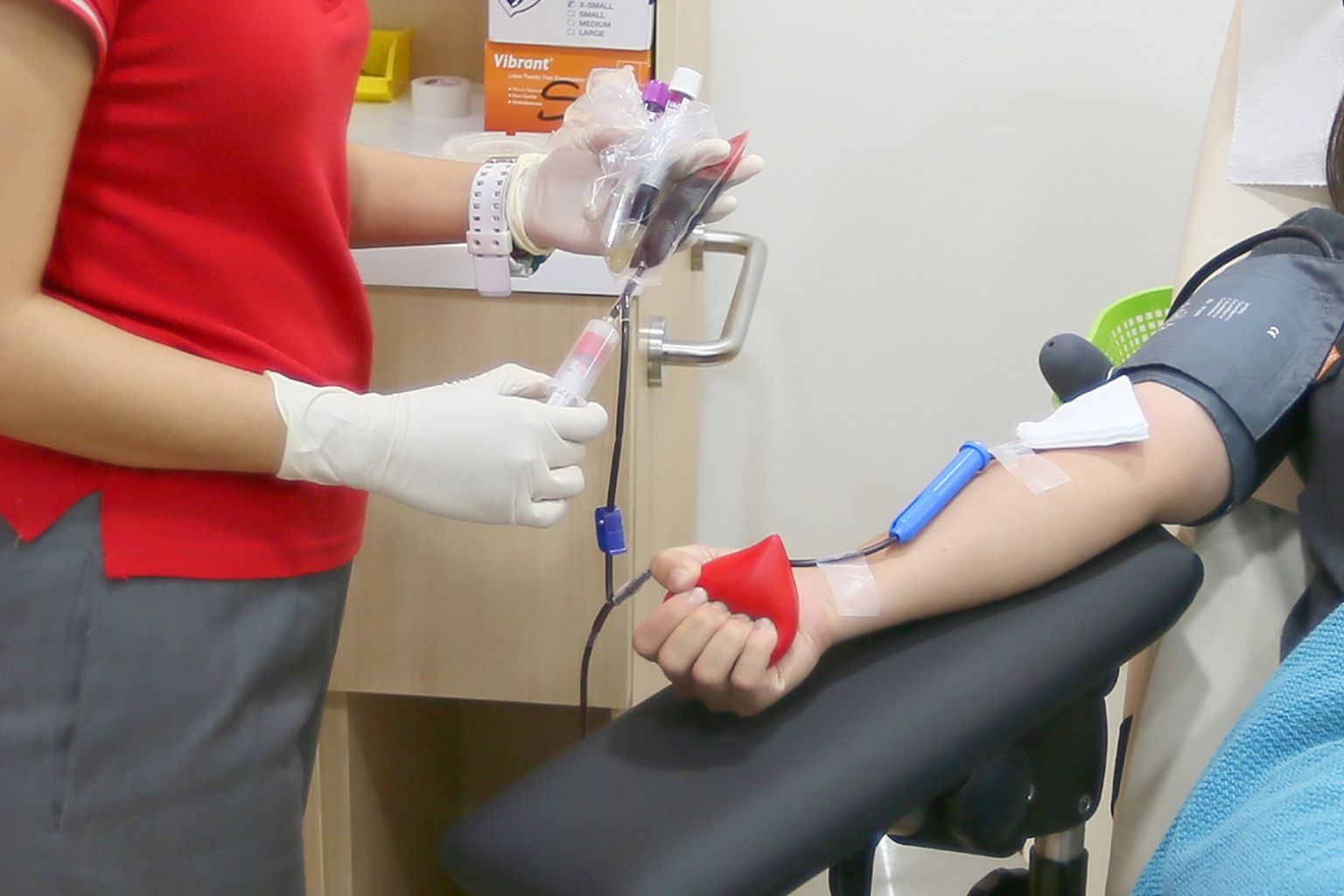
PHOTO: ST FILE
SINGAPORE - The personal information of more than 800,000 blood donors which was put online improperly for over two months was accessed illegally and possibly stolen, a Health Sciences Authority (HSA) vendor responsible for the mistake said on Saturday (March 30).
It was initially thought that only a foreign cyber-security expert, who spotted the vulnerability in the server that stored the data, had accessed it.
However on Saturday, Secur Solutions Group (SSG), an independent vendor of HSA, said its server was also accessed suspiciously from several other IP addresses between October and March this year. It did not say whether these addresses were local or foreign.
A database containing the personal information of blood donors was uploaded to this server around October last year.
This information included the names, NRIC numbers, gender and number of donations of people who have donated or registered to donate blood in Singapore since 1986.
In some cases, donors' blood type, height, weight and the dates of their last three donations were also included.
On March 13, HSA told SSG that a US cyber-security expert had found that the registration-related information of donors could be accessed because of a vulnerability in the server used by SSG.
The server was immediately cut off from the Internet and secured, said SSG.
The vendor engaged external cyber-security professionals, KPMG in Singapore, to undertake forensic analysis. It also initiated a thorough review of its IT systems.
Preliminary examination had found that the unauthorised access was made by only the US cyber-security expert, who said he did not intend to disclose the database and was working with the authority to delete the information.
But subsequent forensic analysis revealed that the server was also accessed suspiciously from several other IP addresses between Oct 22, 2018, and March 13 this year.
SSG said in its statement: "Based on this new information, SSG cannot exclude the possibility that registration-related information of donors on the server was exfiltrated."
The vendor added that the database contains no other sensitive, medical or contact information.
SSG said that there had also been attacks on the same server in 2017. However, these were unrelated to the current incident, and there was no evidence to suggest that any HSA data was compromised.
It is continuing its investigations into the matter, and is cooperating fully with the police and HSA.
It also apologised to all the affected blood donors.
In a statement, HSA said that it was aware of the situation, and added that it takes a serious view of the matter, which the police are investigating.
The agency said that SSG is in breach of its contractual obligations and it will decide on what steps it should take regarding SSG once investigations are concluded.
HSA added that its centralised blood bank system, which is not connected to the SSG server, remains secure.
Public servant Ryan See, 25, who donates blood regularly, said: "I'm not really too concerned about my details getting leaked, but I have been getting quite a few random SMSes asking if I'd like to gamble online. I'm not sure if they're related."
Another regular donor, 19-year-old student Megan Koh, said: "I think it's worrying that these sort of data leaks keep happening, especially since we're increasingly reliant on technology these days and all our data is online."
This is the third IT incident to strike the healthcare sector in recent months.
In January, the Ministry of Health (MOH) revealed that the confidential information of 14,200 HIV-positive individuals had been leaked online by Mikhy Farrera-Brochez, an American who had been living in Singapore.
And in February, MOH said that a computer error had resulted in 7,700 people receiving inaccurate healthcare subsidies when they applied for or renewed their Community Health Assist Scheme cards in September and October last year.
Mr Aloysius Cheang, Asia-Pacific executive vice-president of the Centre for Strategic Cyberspace + Security Science, a London-based think-tank, agreed that the frequency of the recent data leaks was indeed worrying.
"This is not the first time, it's the third time. And when there's a third time, there's bound to be a fourth, a fifth, and so on," he said.
He added that there is a need for Singapore to send a strong signal that its sovereign control over its digital assets has not been compromised, especially since the nation prides itself on being a safe and secure place to do business.
"You have to show people you can protect these things. If you can't even protect your own citizens' data, how can you be trusted to protect that of companies like Google, Amazon, and private banks?"
Dr Ngair Teow-Hin, chief executive officer of data security company SecureAge Technology, said that there is nothing blood donors who may have had their information accessed can do.
"You can't change your NRIC number or date of birth, that's the unfortunate reality of the situation," he said.
He noted that some of the information that was stored in the server, such as the NRIC number and date of birth of donors, is sometimes used by services such as banks and telephone companies to verify one's identity.
Such information could be sold on the Dark Web, or used to impersonate donors.
Both experts said there was a need for harsher penalties to ensure such a mistake does not occur again.
"It's not so much an IT security issue as it is an organisational failure," said Mr Cheang.


