Why some OCBC customers in SMS scams did not get OTPs
Sign up now: Get ST's newsletters delivered to your inbox
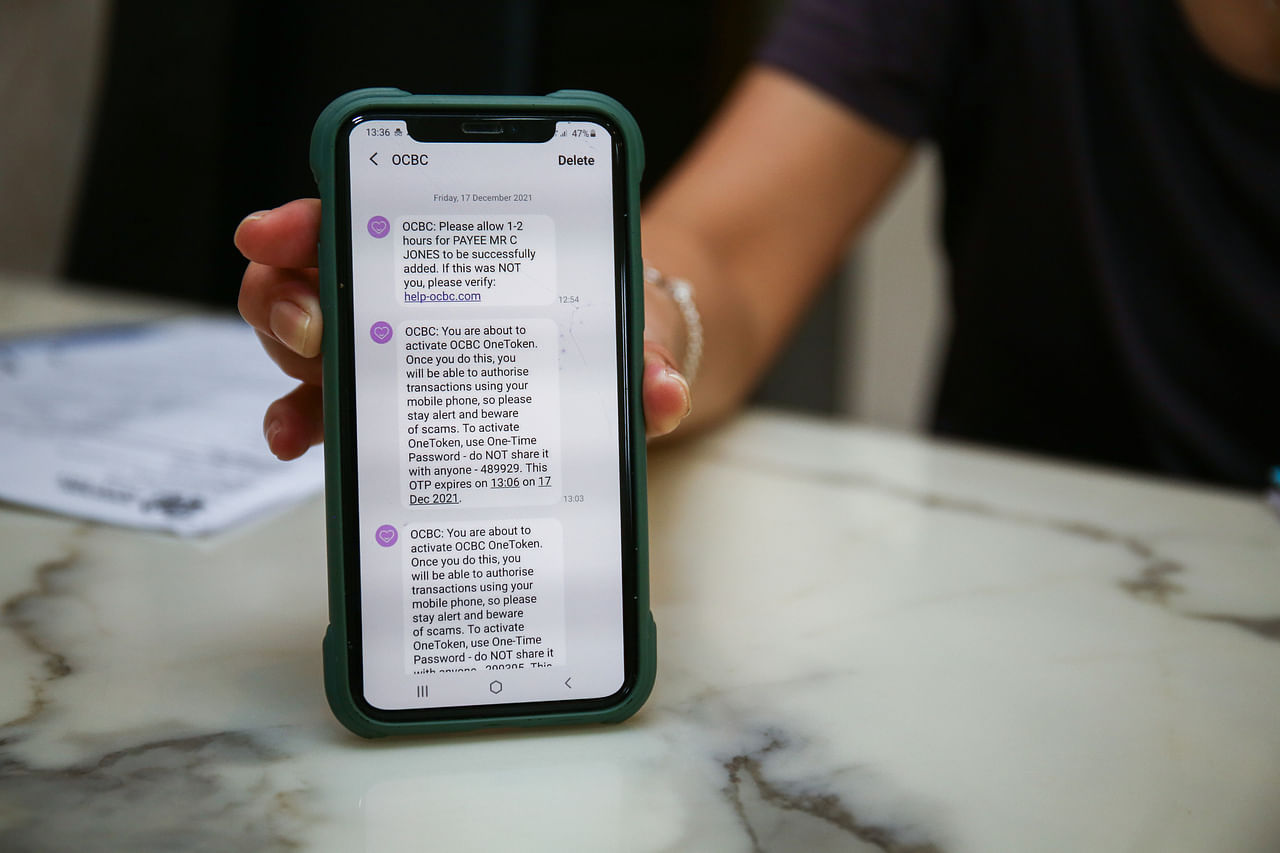
Victims reportedly fell for the ruse because the fake SMSes were grouped by their phones with legitimate SMSes.
PHOTO: LIANHE ZAOBAO FILE
SINGAPORE - Some OCBC Bank customers who lost money in the recent SMS scams were puzzled that they did not get one-time passwords (OTPs) in SMSes sent by the bank to verify the unauthorised transactions.
One possible explanation from OCBC is that the bank's digital authentication tool to verify transactions was activated on the scammers' phones with banking details phished from victims.
Cyber-security experts said it was possible that the SMS OTPs were intercepted by malware on victims' phones, or were diverted to overseas telcos that had been hacked.
Nearly 470 customers lost at least $8.5 million in fraudulent fund transfers in December last year after scammers spoofed the name OCBC uses in its SMSes and sent SMSes to victims with links to phishing sites.
Many victims reportedly fell for the ruse because the fake SMSes were grouped by their phones with legitimate SMSes previously sent by the bank for OTPs and transaction alerts.
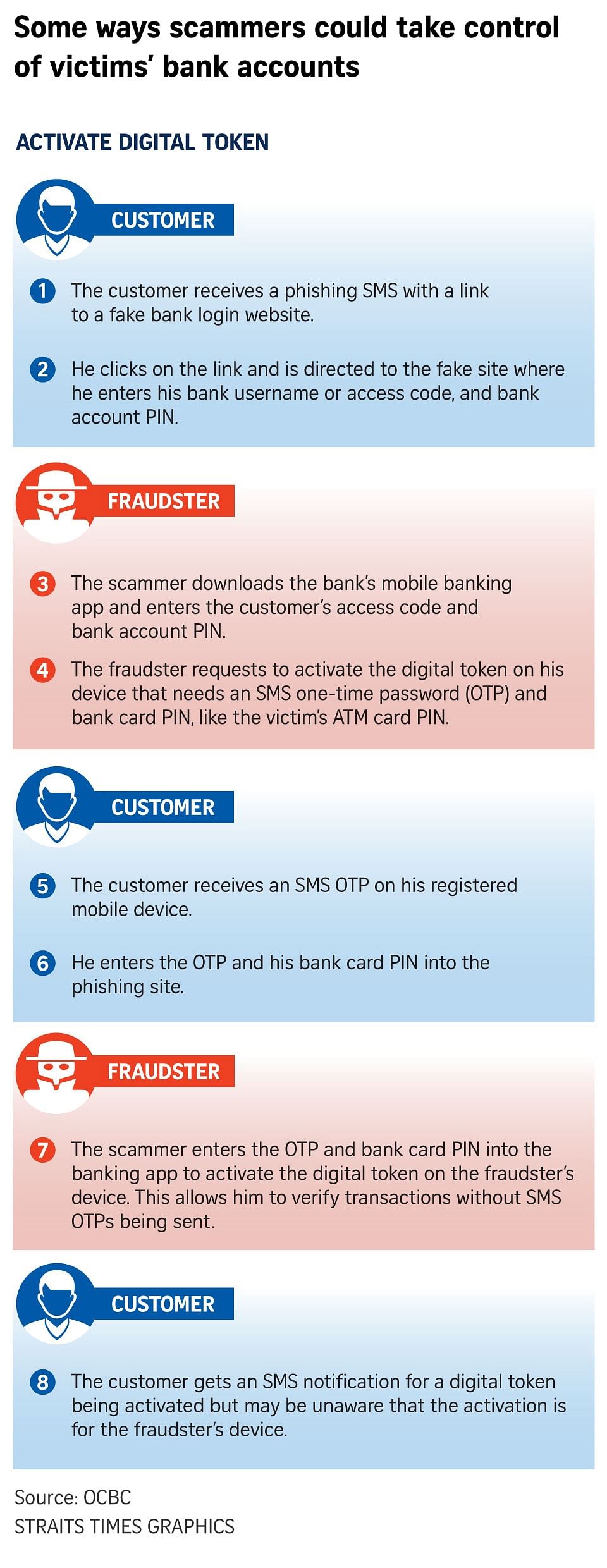
One ruse involves using the bank's digital authentication process in which a customer receives a phishing SMS with a link to a fake bank login website, the bank said on Monday (Jan 17).
When the customer enters his bank username or access code and bank account PIN on the fake site, the scammer steals these details and keys them into the bank's mobile banking app on his device. This allows him to perform multiple transactions up to the daily transfer limit.
The scammer then activates OCBC's OneToken, used for authenticating digital banking transactions, on the banking app. This triggers the sending of an SMS OTP to the customer's registered mobile phone, where he is then prompted by the phishing site to enter with his bank card PIN.
With the token activated, the crook can extract more money from the victim's compromised account by adding local and overseas recipients of funds, as well as raising the daily transfer limit.
The scammer can verify fund transfers by replying to a prompt on the banking app without any SMS OTPs, so the victim does not get an SMS.
However, the customer could get an SMS notification for a digital token being activated but may be unaware that the activation is for the fraudster's device.
Cyber-security expert Anthony Lim, who is also a fellow at the Singapore University of Social Sciences, said it is possible that some victims' banking details were phished in previous attempts.
Malware on the victims' phones may have deleted the messages, postulated Mr Kevin Reed, chief information security officer of cyber-security firm Acronis.
The Association of Banks in Singapore had warned in 2015 about malware on mobile phones that let hackers intercept SMS OTPs and use them for fraudulent transactions.
Mr Reed said this is more likely to happen on Android phones where apps could request SMS access, although iPhones could be vulnerable if there is a flaw in the mobile operating system.
Crooks could also have hacked into victims' bank accounts with stolen login details, and changed the phone numbers associated with the accounts so that SMS OTPs are delivered to the hacker instead of the account holder.
But some banks may have measures against this, said Mr Reed, such as requiring a physical visit to the bank, having a cool-down period, or sending notifications of the change to both the new and old phone numbers so that the owner of the latter can reverse the change if it is malicious.
In some cases, scammers might turn off notifications, so victims do not get alerts on fraudulent transactions, he said.
Hackers could also delay or delete SMSes by breaching the SS7 mobile phone network, a mobile infrastructure for data management. It allows them to spoof SMS sender names, too.
Hackers could also spoof victims' phone numbers such that they receive a copy of SMS OTPs.
It is possible that some SMS OTPs were diverted abroad by scammers, like what happened in cases the authorities highlighted in September last year.
The crooks hacked into the systems of overseas telcos and used them to change the location information of the mobile phone numbers used by Singapore victims, said Mr Reed.
This tricked Singapore telco networks into thinking the Singapore numbers were roaming overseas on other countries' networks.
So, when banks sent SMS OTPs, these were diverted to the overseas mobile network systems and stolen by the hackers.
The best protection is to "not rely on SMS for strong authentication at all" or to confirm sensitive actions, said Mr Reed.
OCBC advises customers not to click on links in SMSes claiming to direct them to the bank's website. Instead, they should use the bank's official mobile banking app or type www.ocbc.com directly into their Web browsers.
If in doubt, they should call the OCBC hotline on 6363-3333 and not any numbers cited in an SMS.

<p>knocbc18 / ST20220117_202230689142 / Alphonsus Chern // Generic photograph of the OCBC Bank branch at Sixth Avenue 17 January 2022.</p>
PHOTO: ST
Customers can also download the ScamShield app for iOS devices from the authorities to block unsolicited messages and calls.
They should not give sensitive information such as login names, passwords and OTPs to anyone or key them into unverified websites.
Said Mr Lim: "One should typically be suspicious, sceptical or at least not be impatient when dealing with unsolicited messages, especially those pertaining to an important personal asset like a bank account."