US pipeline hacking signals growing cyber-security risk for energy system
Sign up now: Get ST's newsletters delivered to your inbox
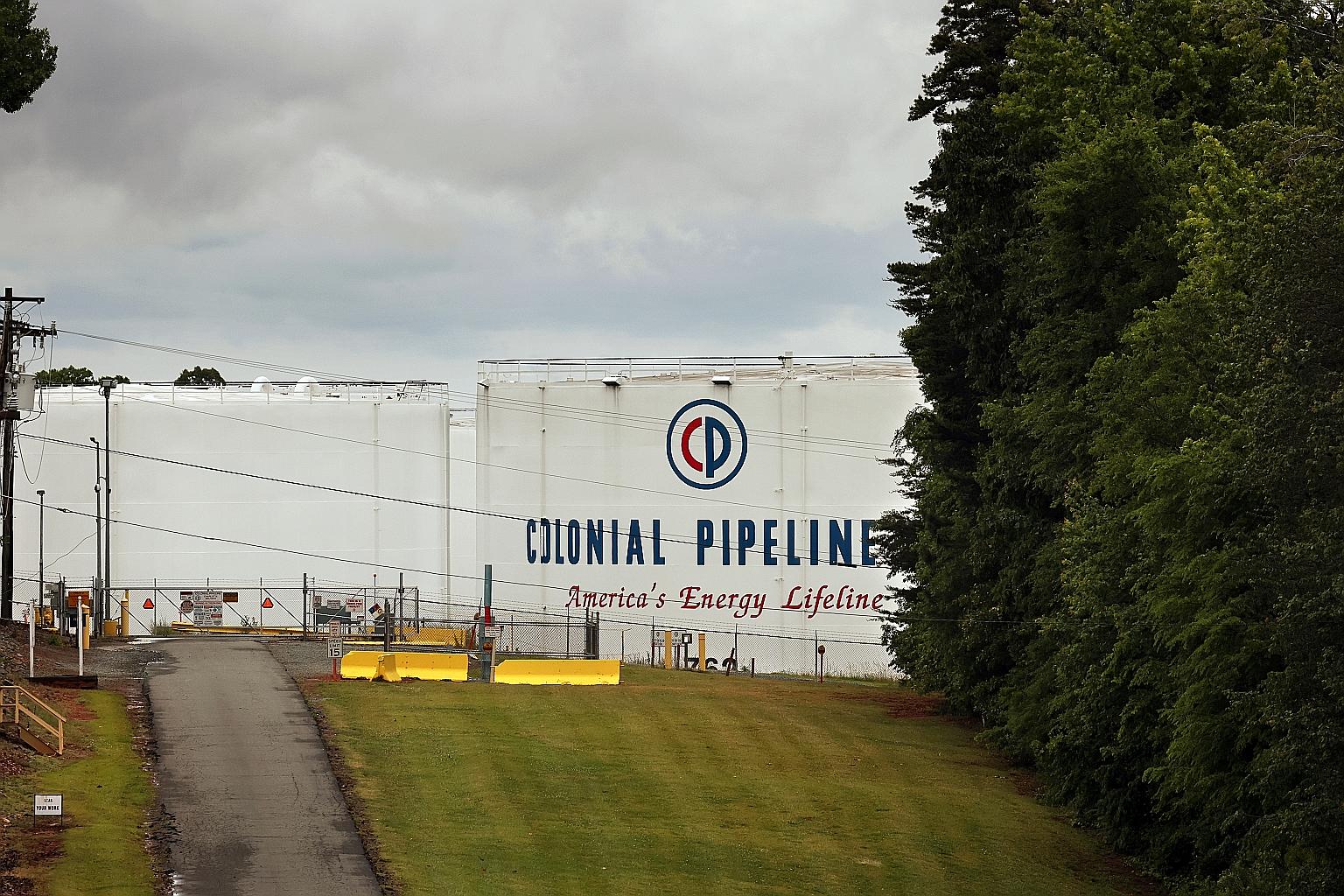
A Colonial Pipeline facility in Charlotte, North Carolina.
PHOTO: NYTIMES
WASHINGTON (NYTIMES) - The audacious ransomware attack that shut down a major fuel pipeline and sent Americans scrambling for petrol in the south-east last week was not the first time that hackers have disrupted the United States' ageing, vulnerable energy infrastructure. And it is unlikely to be the last.
Across the globe, cyber attackers are increasingly taking aim at the energy systems that underpin modern society.
A February report from IBM found that the energy industry was the third-most targeted sector for such attacks last year, behind only finance and manufacturing. That was up from ninth place in 2019.
"This should be a wake-up call," said Mr Jonathon Monken, a principal at energy consulting firm Converge Strategies.
"When you look at what's most likely to cause disruptions to energy companies today, I think you have to put cyber-security risks at the top."
Despite years of warnings, America's vast network of pipelines, electric grids and power plants remains acutely vulnerable to cyber attacks with the potential to disrupt energy supplies for millions of people.
Dealing with those risks, analysts said, will pose a major challenge for the Biden administration as it seeks hundreds of billions of dollars to modernise the nation's energy infrastructure and transition to cleaner sources of energy to address climate change.
Regulators are increasingly poised to step in.
Last week, Mr Richard Glick, the chairman of the Federal Energy Regulatory Commission, said it was time to establish mandatory cyber-security standards for the nation's nearly 4.8 million km of oil and gas pipelines, similar to those currently found in the electricity sector.
"Simply encouraging pipelines to voluntarily adopt best practices is an inadequate response to the ever increasing number and sophistication of malevolent cyber actors," Mr Glick said in a statement.
The risks to the nation's energy systems are widespread and varied. Many oil and gas pipelines, for instance, rely on decades-old control systems that are not well defended against more sophisticated cyber attacks and cannot be easily updated.
And it is not just pipelines. As electric grid operators harness a growing array of digital technologies to help manage the flow of power and cut planet-warming emissions - such as smart thermostats, or far-flung yet interconnected networks of solar arrays - hackers may find new entry points to exploit.
The shutdown on May 7 of the Colonial Pipeline, which stretches 8,850km from Texas to New Jersey and transports 45 per cent of the East Coast's fuel supplies, illustrates how devastating such attacks can be.
On May 8, Colonial acknowledged that its corporate computer systems had been hit by a ransomware attack, in which criminal groups hold data hostage until the victim pays a ransom.

A tanker delivering fuel to a Speedway petrol station in Alexandria, Virginia, last Thursday. A ransomware attack had shut down a major fuel pipeline in America and sent people scrambling for petrol in the south-east last week.
PHOTO: EPA-EFE
The company said that it had shut down the pipeline as a precaution, apparently for fear that the hackers might have obtained information that would enable them to attack parts of the pipeline itself.
Colonial said last Wednesday that it had started to resume pipeline operations, although it would take several days to restore full service. But throughout the south-east, panicked Americans were racing to stock up on petrol, causing thousands of petrol stations to run out of fuel.
While Colonial has yet to explain exactly what triggered the pipeline shutdown, experts said there were plenty of vulnerabilities lurking throughout America's energy infrastructure.
Last year, the Cybersecurity and Infrastructure Security Agency reported a ransomware attack on a natural gas compression facility that caused a shutdown of the facility for two days.
In 2018, several natural gas pipeline operators reported that a system that processes customer transactions had been attacked, leading to service disruptions.
But bigger risks lurk: In 2016, hackers knocked out large sections of the power grid in Ukraine, in what was thought to be the first intentional blackout triggered by a cyber attack.
At the time, the Obama administration warned that America's electric utilities were not immune to similar attacks.
In the past, energy companies typically kept the operational systems that run pipelines or power plants disconnected, or "air gapped", from the broader Internet, which meant that hackers could not easily gain access to the most critical infrastructure.
But increasingly that is no longer the case, as companies install more sophisticated monitoring and diagnostics software that helps them operate these systems more efficiently. That potentially creates new cyber-security risks.
"Now these systems are all interconnected in ways that the companies themselves do not always fully understand," said Mr Marty Edwards, vice-president of operational technology for Tenable, a cyber-security firm.
"That provides an opportunity for attacks in one area to propagate elsewhere."
Many industrial control systems were installed decades ago and run on outdated software, which means that even finding programmers to upgrade the systems can be a challenge.
And the operators of vital energy infrastructure - such as pipelines, refineries or power plants - are often reluctant to shut down the flow of fuel or power for extended periods of time to install frequent security patches.
Making things harder still, analysts said, many companies do not always have a good sense of exactly when and where it is worthwhile to spend money on costly new cyber-security defences, in part because of a lack of readily available data on which types of risks they are most likely to face.
"Companies don't always release a lot of information publicly" about the threats they are seeing, said Mr Padraic O'Reilly, a co-founder of CyberSaint Security, who works with pipelines and critical infrastructure on cyber security.
"That can make it hard as an industry to know where to invest."
Analysts said that the nation's electric utilities and grid operators were typically further ahead in preparing for cyber attacks than the oil and gas industry, in part because federal regulators have long required cyber-security standards for the backbone of the nation's power grid.
Still, vulnerabilities remain.
"Part of it is the sheer complexity of the grid," said Mr Reid Sawyer, managing director of the US cyber-consulting practice at Marsh, an insurance firm.
Not all levels of the grid face mandatory standards, for instance, and there are more than 3,000 utilities in the country with varying cyber-security practices.
Energy companies may never be able to defend themselves against every single potential cyber attack out there, experts said. Instead, businesses and policymakers will need to design broader energy systems that are resilient to attacks and potential shutdowns, by, for instance, building in more redundancies or overrides.
"It's an old saying in cyber security: The people working defence have to be right 100 per cent of the time, while the attackers have to be right only once," Mr Monken said.
"That means we have to think a lot harder about contingencies when those defences fail."


