Ransomware attacks threaten nations, 137 S'pore firms fell prey in 2021: CSA
Sign up now: Get ST's newsletters delivered to your inbox

As not every attack was reported, the figures may represent only the tip of the iceberg.
PHOTO: ST FILE
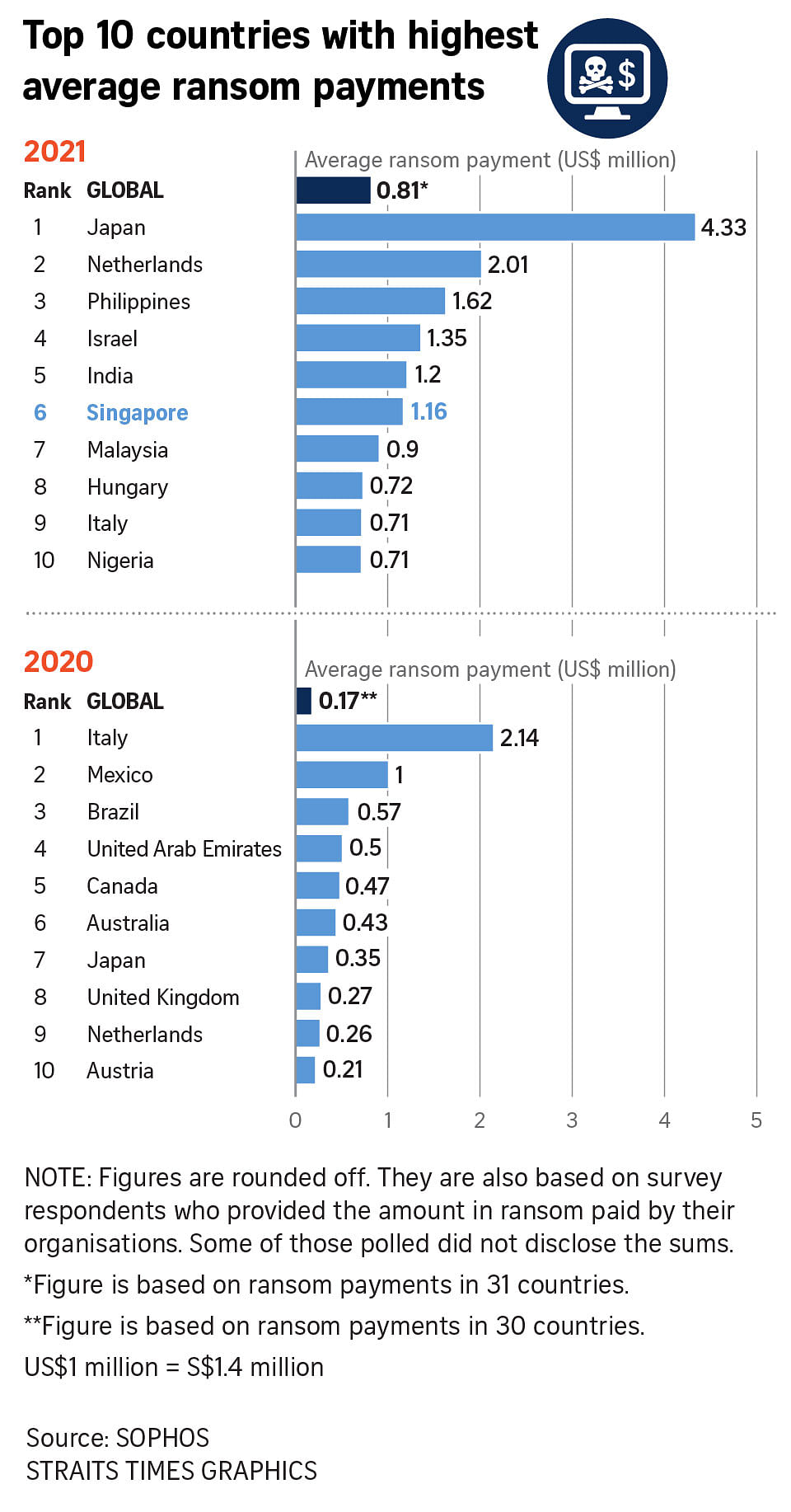
SINGAPORE - Fifty per cent more companies in Singapore fell prey to ransomware last year, as such attacks increasingly become national security threats.
Mirroring global trends, the number of firms in Singapore that had their systems locked up until a ransom was paid shot up from 89 in 2020 to 137 last year, said the Cyber Security Agency (CSA) of Singapore.
"The year saw ransomware attacks 'graduate' fully from sporadic and isolated incidents, into legitimate national security risks capable of massive and systemic attacks affecting entire networks of large enterprises," said CSA in its Singapore Cyber Landscape 2021 report released on Monday (Aug 29).
As not every attack was reported, the figures may very well represent only the tip of the iceberg, the sixth annual report said.
CSA found that a majority of firms here hit by ransomware last year were small and medium-sized enterprises (SMEs) from industries such as IT and manufacturing, said to be "low hanging fruit".
"These two sectors often run 24/7 operations and may not be able to afford the downtime to patch their systems," said the agency.
It said several groups that targeted Singapore SMEs use the ransomware-as-a-service model, where hackers lease malicious software to other cyber criminals in exchange for a cut of the proceeds. This model significantly lowers the barrier to entry for amateur or less-skilled hackers to attack companies.
Although the report did not provide specific Singapore cases in detail, it mentioned a data breach last January involving the personal information about 129,000 Singtel customers as a result of a ransomware attack.
Hackers exploited vulnerabilities in US tech firm Accellion's file-sharing software, which is used by Singtel and many global firms. Cyber criminals later posted a ransom note addressed to Accellion demanding $250,000 worth of bitcoin. The incident shone the spotlight on supply chain risks.
Other high-profile global incidents include an attack on American fuel transporter Colonial Pipeline's IT systems in May last year, which affected its oil and gas supply to about 50 million customers, leading to fuel shortages and price hikes.
Ireland's Health Service Executive and New Zealand's Waikato District Health Board were also hit by ransomware in May last year, which caused sensitive patient data to be leaked and the shutdown of the organisations' systems that disrupted essential healthcare services.
One of the world's largest meat producers, JBS, temporarily suspended operations at its processing plants in North America and Australia, after a ransomware attack in June last year shut down its IT network. The move threatened to disrupt global food supply chains and further inflate food prices. It later paid US$11 million ($15.3 million) to criminals to restore its data.
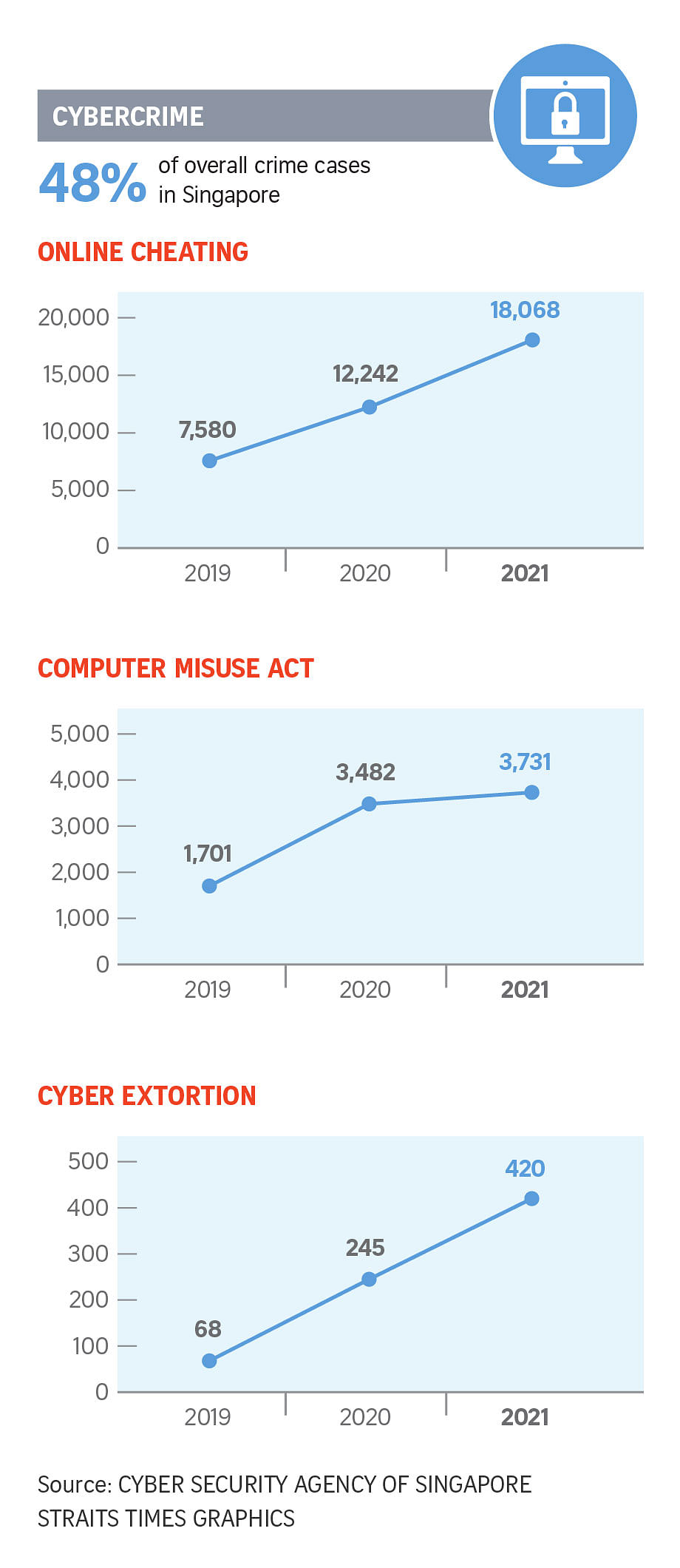
Also mirroring global trends, there was a three-fold increase in the number of command and control servers controlled by hackers hosted here - from 1,026 in 2020 to 3,300 last year, said CSA.
These servers control malware-infected computers or surveillance cameras to launch attacks that steal data, distribute ransomware or take down critical systems.
CSA said phishing remained a popular method for hackers to gain access into systems before deploying malware in them. There were 55,000 links to phishing sites hosted here last year, a 17 per cent increase from 47,000 in 2020.
Social networking firms such as WhatsApp and Facebook made up more than half of spoofed targets last year. Scammers took advantage of public interest in WhatsApp's announcement last January on how its users' phone numbers would be shared with Facebook.
In Singapore, spoofed phishing SMSes sent out by scammers in December last year resulted in 790 OCBC Bank customers losing about $13.7 million.
CSA said in its report that the Ministry of Health was the most commonly spoofed government agency, with impersonations growing substantially as Covid-19 cases surged in the fourth quarter of last year. Other notable agencies were CSA and the Ministry of Manpower."In most of these cases, scammers spoofed the authorities to trick victims into divulging their credentials or personal data," said CSA.
Significant cyber security incidents in 2021
Global incidents:
January
- Vulnerabilities in American tech firm Accellion’s software exploited and used for data breaches and extortions
January to March
- Hack of a widely-used Microsoft e-mail server software
February
- Attempted poisoning of the water supply in Florida, US via cyberattack
May
- Ransomware attack on American fuel supplier Colonial Pipeline
- Ransomware attack on JBS, one of the world’s largest meat producers
July
- Vulnerability in tech firm Kaseya’s software used for ransomware attacks
- Israeli firm NSO Group’s spyware revealed to be have been used against government officials and journalists
- Cyberattack on Iran’s train system
August
- Alleged targeting of South-east Asian telcos by hacker groups typically backed by governments
November
- Cyberattack on Iran’s gas stations
- Cyberattacks involving malware Emotet return after most of its infrastructure was dismantled by law enforcement operations in Jan 2021
December
- Security flaw in software Log4j used for cyberattacks
Incidents in Singapore:
January
- Data breach involving personal information of Singtel’s customers
March to August
- Various companies suffer ransomware attacks and data extortion by hacking group Altdos
July
- Data breach involving personal information of Starhub’s customers
August
September
- Statement by authorities that criminals are able to obtain SMS one-time passwords (OTPs) sent by banks to make fake credit card payments
November
- Cyberattack with data theft on marine services provider Swire Pacific Offshore
December
- High-profile phishing scams targeting OCBC Bank customers


