Singapore critical sectors, government not affected by NotPetya ransomware
Sign up now: Get ST's newsletters delivered to your inbox
Singapore was not affected by the "NotPetya" ransomware attack that first emerged on June 27.
PHOTO: AFP
SINGAPORE -Singapore has emerged relatively unscathed in the latest round of ransomware attacks, a month after WannaCry hit organisations around the world.
After "NotPetya" first emerged on Tuesday (June 27), there has been no report on NotPetya ransomware infection in Singapore, said Singapore's Cyber Security Agency (CSA) and GovTech on Wednesday (June 28).
"None of Singapore's 11 critical information infrastructure sectors were affected; our government systems have not been affected... The Singapore government is closely monitoring the global situation," said the joint statement.
GovTech said it has also put in place measures which minimises the likelihood of government systems being infected by malware, including ransomware.
However, the Singapore office of some international companies including British advertising giant WPP was affected. Some Singapore staff of WPP's ad agencies The Straits Times spoke to said they received an internal memo on Wednesday (June 28) via e-mail informing them to shut down all computers.
"WPP is mandating that everyone immediately shut down all computers, both Macs and PCs. This applies to you whether you are in the office or elsewhere. Working on an office computer remotely is not an option," according to the internal memo. As a precaution, some staff did not turn on their office computer and instead used their personal computer to work. Some also worked from home on Wednesday (June 28). WPP's website was also down.
When contacted, WPP would only say: "Our operations have not been uniformly affected, and issues are being addressed on a company-by-company basis. Many of our businesses are experiencing no or minimal disruption."
WPP also said it is working with its IT partners and law enforcement agencies "to take all appropriate precautionary measures, restore services where they have been disrupted, and keep the impact on clients, partners and our people to a minimum".
The New Paper also reported that courier company TNT Express (Singapore) was also affected. Staff here received an internal memo not to turn on their computers or unplug them.
Organisations, businesses and members of the public can refer to the advisory for the steps that they can take to prevent or recover from ransomware on www.csa.gov.sg/singcert or contact SingCERT at singcert@csa.gov.sg or the hotline at 6323-5052 for assistance.
Systems integrators told The Straits Times that many organisations have patched their vulnerable systems following the WannaCry scare last month. This could have contributed to their narrow escape from the latest round of disaster that struck governments, ad agencies and port operators globally.
NotPetya is said to be more dangerous and intrusive than WannaCry, which subsided after a kill switch was accidentally applied last month (2017). This prompted experts to warn that the worst is yet over.
Mr Jeffrey Kok, CyberArk's technical director of Asia-Pacific and Japan, said: "It is hard to predict NotPetya's impact on Singapore and Asia just yet; NotPetya is more potent than WannaCry and does not have a kill switch."
NotPetya, a variant of the Petya ransomware that first surfaced in March last year (2016), is expected to continue to infect vulnerable systems missed by WannaCry, Mr Kok added.
NotPetya and WannaCry infect computers using the same hacking tool, dubbed Eternal Blue, used by the National Security Agency. Eternal Blue was leaked online in April this year by a group of hackers known as the Shadow Brokers.
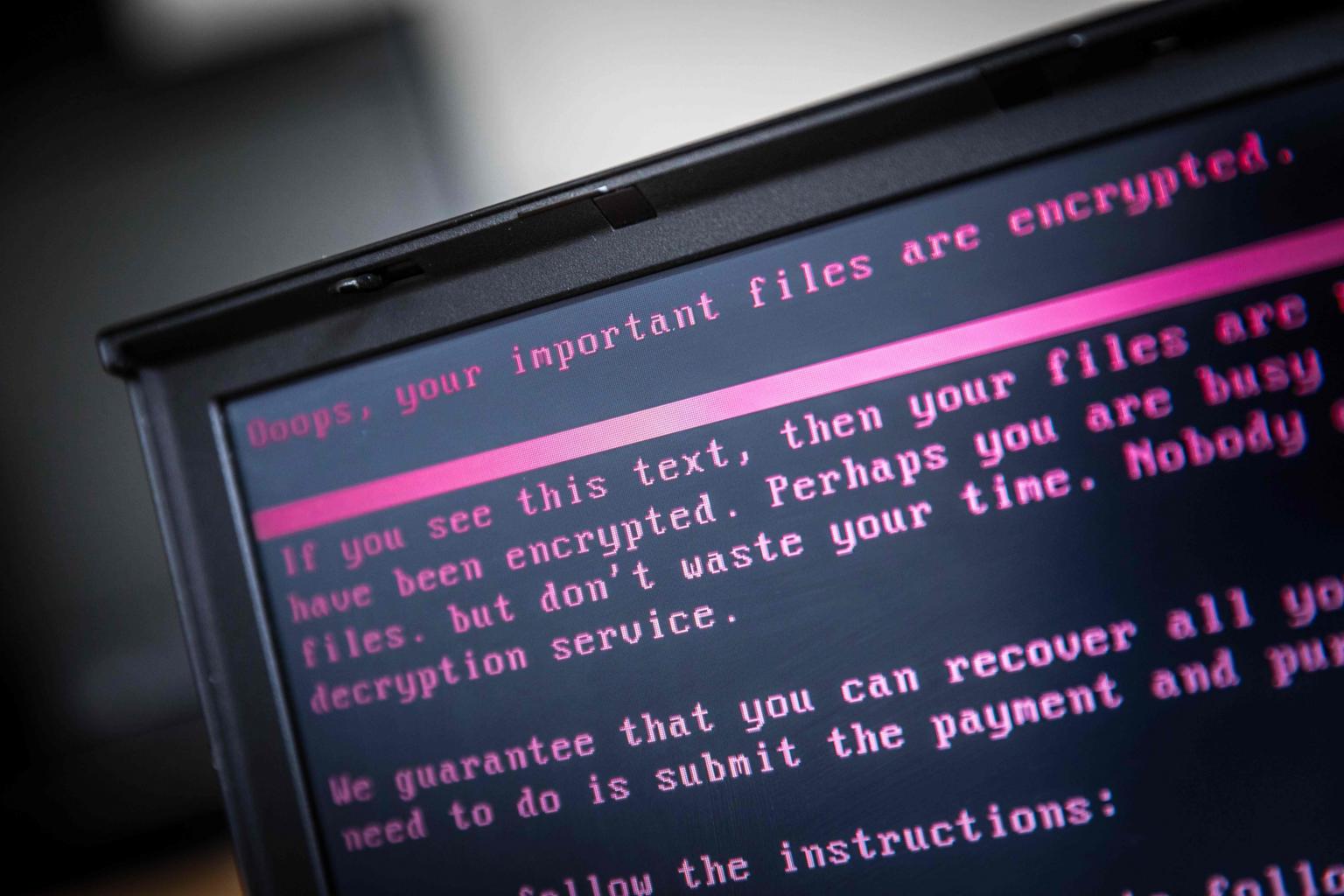
Unsuspecting e-mail users who click on infected Office document attachments will unleash the NotPetya worm, and cause it to spread to other connected computers. Infected systems were then locked down with a note demanding a ransom of US$300 (S$416) in cryptocurrency per infected computer to unlock the hostage data.
Russia's top oil producer Rosneft and the Ukrainian government were among the first to be hit by NotPetya, followed by organisations in France, Spain, Britain, the United States, Australia and India.
India's largest container operation - the Jawaharlal Nehru Port Trust, operated by Danish shipping firm A.P. Moller-Maersk - was reportedly disrupted, while production at Cadbury chocolate factory on the island state of Tasmania ground to a halt lafter computer systems went down on Tuesday (June 27).
British advertising giant WPP's website was also down.
Mr Steve Ledzian, senior director of systems engineering at FireEye, a security systems specialist, said that the malware came from a software supplier that Ukrainian businesses rely on to manage tax accounting.
"Businesses need to realise that their security perimeter extends to those organisations they depend on," he said.
To minimise their exposure to destructive malware, organisations should promptly install software updates and patches, he said.
Critical files must be also be backed up daily, and the copies encrypted and kept offline.
Experts have also advised affected users against paying the ransom. Said Mr Nick Fitzgerald, security software maker ESET Asia-Pacific's senior research fellow: "People shouldn't pay for the ransom as they will not be able to receive the decryption key."


