Cyberattack reaches Asia and Australia as new targets hit by ransomware demand
Sign up now: Get insights on Asia's fast-moving developments

The spread of the attack across the globe and into Asia and Australia underscores how ransomware is becoming a routine risk of doing business.
PHOTO: REUTERS
LONDON (BLOOMBERG, REUTERS) - A new cyberattack similar to WannaCry has reached Asia after spreading from Europe to the US overnight, hitting businesses, port operators and government systems.
A terminal operated by A.P. Moller-Maersk at the Jawaharlal Nehru Port Trust, a facility near Mumbai which is India's biggest container port, was unable to load or unload because of the attack.
With the Gateway Terminal India facility unable to identify which shipment belongs to whom, the port is clearing cargo manually, Chairman Anil Diggikar said in a phone interview.
After wreaking havoc in Europe, the attackers behind the Petya virus have had a limited impact in Asia so far as they demand users pay US$300 (S$416) in cryptocurrency per infected computer to unlock their systems.
About 2,000 users had been attacked as of midday on Tuesday in North America, according to Kaspersky Lab analysts, with organisations in Russia and Ukraine the most affected.
India-based employees at Beiersdorf, makers of Nivea skin care products, and Reckitt Benckiser, which owns Enfamil and Lysol, also told Reuters the ransomware attack had impacted some of their systems in the country.
Meanwhile, a Cadbury chocolate factory became the first Australian business to be hit by the global attack, a trade union official said. Production at the Cadbury factory on the island state of Tasmania ground to a halt late on Tuesday after computer systems went down, said Australian Manufacturing and Workers Union state secretary John Short.
Factory workers "weren't sure what it was but, as the night's gone on, they've realised there's been some significant attacks around the world", Short told Reuters.
Cadbury owner Mondelez International Inc said in a statement released overnight staff in various regions were experiencing technical problems but it was unclear whether this was due to a cyberattack. A Mondelez spokeswoman in Australia had no immediate comment.
There are signs the virus is starting to spread in China but no large-scale outbreak has been detected, according to Zheng Wenbin, chief security engineer at Qihoo 360 Technology Co.
The spread of the attack across the globe and into Asia and Australia underscores how ransomware is becoming a routine risk of doing business. While banks and retailers have strengthened their defences against certain types of attacks, such as those aimed at stealing credit card data, many other enterprises are still catching up in guarding against ransomware.
About 2,000 users had been attacked as of midday Tuesday in North America, according to Kaspersky Lab analysts, with organisations in Russia and the Ukraine the most affected.
"With there being no global kill switch for this one, we'll continue to see the numbers rise in different parts of the world as more vulnerable systems become more exposed," said Beau Woods, deputy director of the Cyber Statecraft Initiative at the Atlantic Council in Washington.
The attack popped up in government systems in Kiev, then disabled operations at companies including Rosneft PJSC, advertiser WPP Plc and the Chernobyl nuclear facility. More than 80 companies in Russia and Ukraine were initially affected, Moscow-based cybersecurity company Group-IB said.
DLA Piper Rob Wainwright, executive director at Europol, said the agency is "urgently responding" to reports of the new cyber attack. In a separate statement, Europol said it's in talks with "member states and key industry partners to establish the full nature of this attack at this time."
Kremlin-controlled Rosneft, Russia's largest crude producer, said in a statement that it avoided "serious consequences" from the "hacker attack" by switching to "a backup system for managing production processes."
British media company WPP's website is down, and employees have been told to turn off their computers and not use Wi-Fi, according to a person familiar with the matter. Sea Containers, the London building that houses WPP and agencies including Ogilvy & Mather, has been shut down, another person said. "IT systems in several WPP companies have been affected," the company said in emailed statement.
Law firm DLA Piper took down its systems as a "precautionary measure" as it dealt with the attack, meaning clients couldn't contact its team by email or land-line, according to a notice on its website The most vulnerable places are "where the operators are a lot of the times at the mercy of manufacturers and providers of those technologies and there's a long time between existence of a fix and implementation of a fix," Woods said.
GLOBAL ATTACK
The hack quickly spread from Russia and the Ukraine, through Europe and into the US. A.P. Moller-Maersk said its customers can't use online booking tools and its internal systems are down. The attack is affecting multiple sites and units, which include a major port operator and an oil and gas producer, spokeswoman Concepcion Boo Arias said by phone.
APM Terminals, owned by Maersk, is experiencing system issues at multiple terminals, including the Port of New York and New Jersey, the largest port on the US East Coast, and Rotterdam in The Netherlands, Europe's largest harbour. APM Terminals at the Port of New York and New Jersey will be closed for the rest of the day "due to the extent of the system impact," the Port said.
Cie de Saint-Gobain, a French manufacturer, said its systems had also been infected, though a spokeswoman declined to elaborate, and the French national railway system, the SNCF, was also affected, according to Le Parisien. Merck & Co Inc, based in Kenilworth, New Jersey, reported that its computer network was compromised due to the hack.
Port operators at grain terminals in Rosario, Argentina also reported the attack affected operations, including halting some deliveries, beginning Tuesday morning, according to Guillermo Wade, manager of the Rosario port and maritime chamber.
WANNACRY WARNINGS
The strikes follow the global ransomware assault involving the WannaCry virus that affected hundreds of thousands of computers in more than 150 countries as extortionists demanded US$300 in bitcoin from victims. Ransomware attacks have been soaring and the number of such incidents increased by 50 per cent in 2016, according to Verizon Communications Inc.
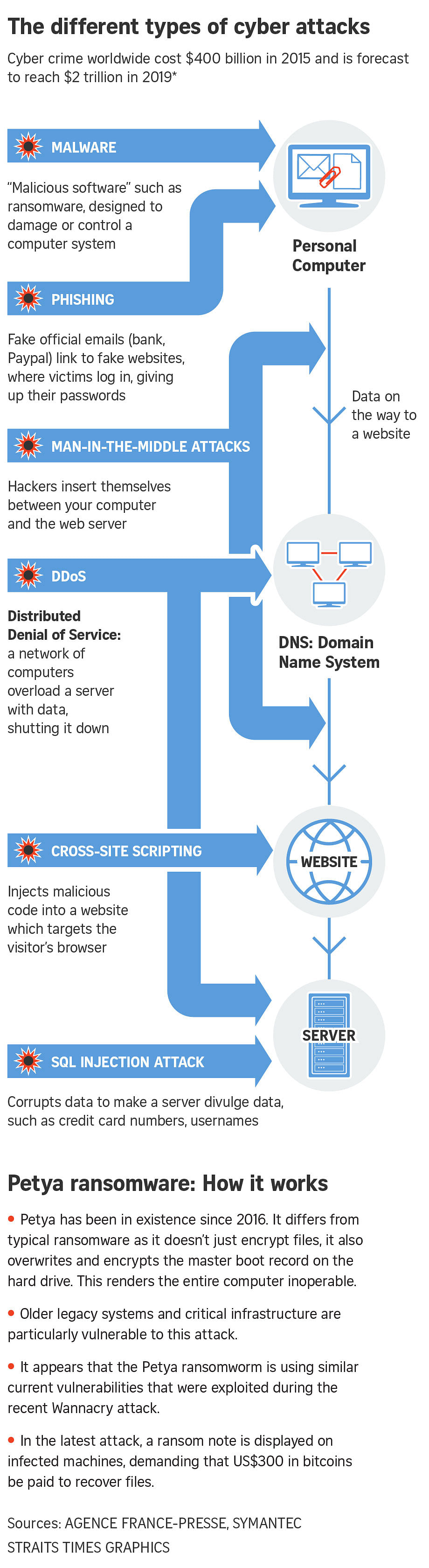
Analysts at Symantec Corp, have said the new virus, called Petya, uses an exploit called EternalBlue to spread, much like WannaCry. EternalBlue works on vulnerabilities in Microsoft Corp's Windows operating system.
The new virus has a fake Microsoft digital signature appended to it and the attack is spreading to many countries, Costin Raiu, director of the global research and analysis team at Moscow-based Kaspersky Lab, said on Twitter.
The attack has hit Ukraine particularly hard. The intrusion is "the biggest in Ukraine's history," Anton Gerashchenko, an aide to the Interior Ministry, wrote on Facebook. The goal was "the destabilisation of the economic situation and in the civic consciousness of Ukraine," though it was "disguised as an extortion attempt," he said.
Kyivenergo, a Ukrainian utility, switched off all computers after the hack, while another power company, Ukrenergo, was also affected, though "not seriously," the Interfax news service reported.
Ukrainian delivery network Nova Poshta halted service to clients after its network was infected, the company said on Facebook. Ukraine's Central Bank warned on its website that several banks had been targeted by hackers.


