SINGAPORE - The Singapore Computer Emergency Response Team (SingCert) has issued an alert to computer users to patch their Microsoft Windows computers, which are the targets of the latest ransomware dubbed Petya.
SingCert, a unit of Singapore's Cyber Security Agency (CSA), said users of these Windows machines should also ensure that their anti-virus software is updated with the latest malware definitions. "Users should perform file backups and store them offline in case they need to restore their systems following an attack," it added on Wednesday (June 28).
Windows operating systems believed to be vulnerable to the ransomware include:
•Windows 10
•Windows RT 8.1
•Windows 8.1
•Windows 7
•Windows XP
•Windows Vista
•Windows Server 2016
•Windows Server 2012 and Window Server 2012 R2
•Window Server 2008 and Windows Server 2008 R2
On Tuesday (June 27), SingCert was alerted to the global spread of a ransomware inspired by WannaCry, which infected hundreds of thousands of computers in about 150 countries and disrupted healthcare and government sectors there in May (2017).
In Singapore, digital signage in some malls supplied by local firm MediaOnline broke down, and computers tied to some 500 Internet accounts were believed to have been infected by WannaCry - although critical sectors like finance, telecommunications and energy emerged relatively unscathed.
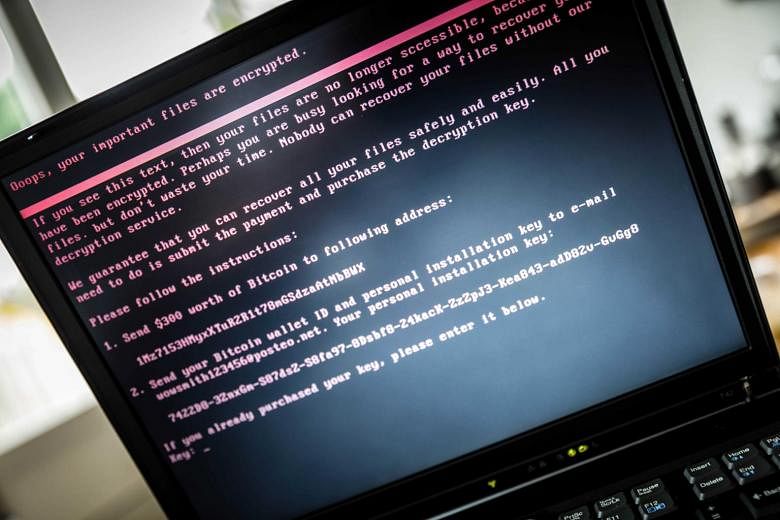
SingCert described Petya as "more dangerous and intrusive" than WannaCry; Petya encrypts the entire hard drive rather than each file individually. Petya spreads via e-mail with booby-trapped Office documents. The documents, once opened, will download and run the Petya installer and execute the worm to spread to other connected computers.